Radar now tracks post-quantum encryption support on origin servers, provides a tool to test any host for post-quantum compatibility, and introduces a Key Transparency dashboard for monitoring end-to-end encrypted messaging audit logs.
Post-quantum origin support
The new Post-Quantum API provides the following endpoints:
/post_quantum/tls/support– Tests whether a host supports post-quantum TLS key exchange./post_quantum/origin/summary/{dimension}– Returns origin post-quantum data summarized by key agreement algorithm./post_quantum/origin/timeseries_groups/{dimension}– Returns origin post-quantum timeseries data grouped by key agreement algorithm.
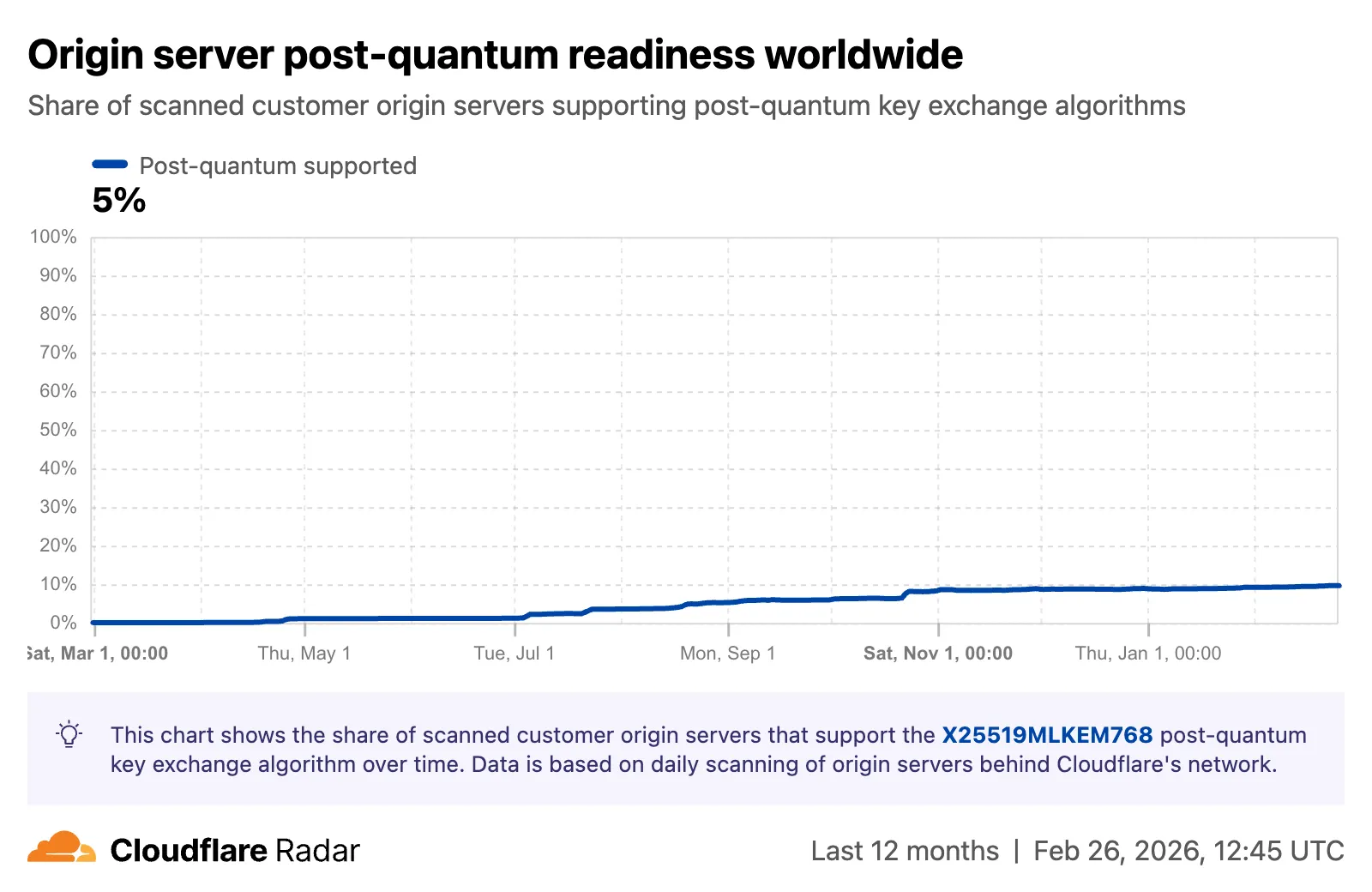
The new Post-Quantum Encryption page shows the share of customer origins supporting X25519MLKEM768, derived from daily automated TLS scans of TLS 1.3-compatible origins. The scanner tests for algorithm support rather than the origin server’s configured preference.
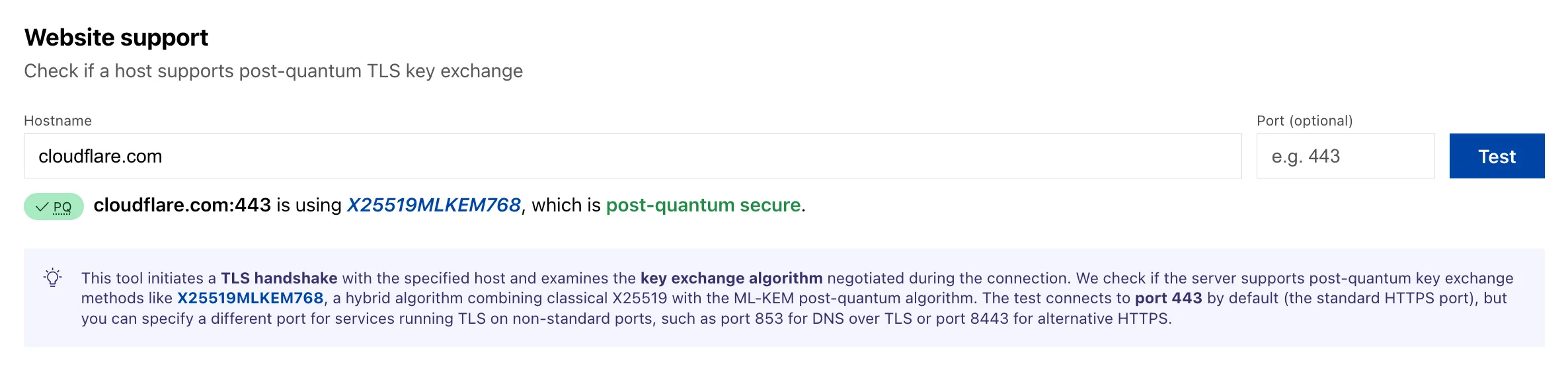
A host test tool allows checking any publicly accessible website for post-quantum encryption compatibility. Enter a hostname and optional port to see whether the server negotiates a post-quantum key exchange algorithm.
Key Transparency
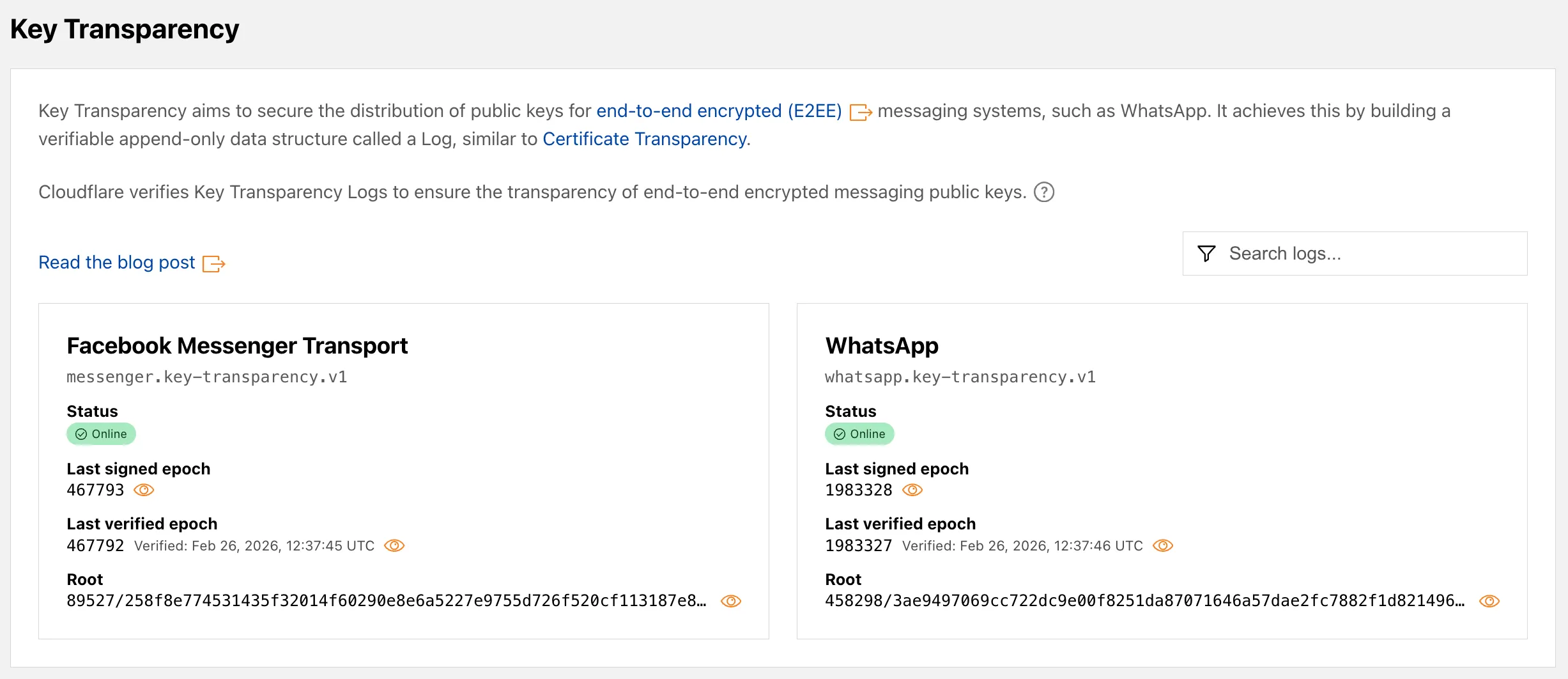
A new Key Transparency section displays the audit status of Key Transparency logs for end-to-end encrypted messaging services. The page launches with two monitored logs: WhatsApp and Facebook Messenger Transport.
Each log card shows the current status, last signed epoch, last verified epoch, and the root hash of the Auditable Key Directory tree. The data is also available through the Key Transparency Auditor API.
Learn more about these features in our blog post and check out the Post-Quantum Encryption and Key Transparency pages to explore the data.
Source: Cloudflare
Latest Posts
- GCP Release Notes: May 05, 2026

- 4 new Qwen models for multimodal reasoning, agentic coding, and multilingual applications are now available in Amazon SageMaker JumpStart

- Data Privacy: Microsoft Online Services Subprocessor Disclosure [MC1301809]
![Data Privacy: Microsoft Online Services Subprocessor Disclosure [MC1301809] 4 pexels anthony derosa 39577 211816](data:image/svg+xml;base64,PHN2ZyB3aWR0aD0iMSIgaGVpZ2h0PSIxIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciPjwvc3ZnPg==)
- Microsoft 365 Copilot Cowork: Plugins, connectors, and partner integrations (Frontier) [MC1301832]
![Microsoft 365 Copilot Cowork: Plugins, connectors, and partner integrations (Frontier) [MC1301832] 5 pexels jplenio 1118873](data:image/svg+xml;base64,PHN2ZyB3aWR0aD0iMSIgaGVpZ2h0PSIxIiB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciPjwvc3ZnPg==)



![Data Privacy: Microsoft Online Services Subprocessor Disclosure [MC1301809] 4 pexels anthony derosa 39577 211816](https://mwpro.co.uk/wp-content/uploads/2024/08/pexels-anthony-derosa-39577-211816-150x150.webp)
![Microsoft 365 Copilot Cowork: Plugins, connectors, and partner integrations (Frontier) [MC1301832] 5 pexels jplenio 1118873](https://mwpro.co.uk/wp-content/uploads/2024/08/pexels-jplenio-1118873-150x150.webp)

